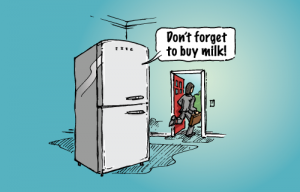
 I have talked before about the coming Internet of Things and the changes it will bring. The Internet of Things or IoT is a term coined by Cisco to describe the interconnected nature of devices that are linked to each other and to the Internet or an intranet. Imagine a future where your car communicates with your refrigerator and your oven and your home heating, security, and entertainment systems. On your way home from work your car automatically detects your intended destination and communicates with your refrigerator to release your dinner to the oven. By the time you arrive home the lights are on, your security system has unlocked the door, and dinner is on the table, with soft music playing to soothe you after your hectic day. This is all well and good but it will require a lot of work in the background to embed all of these things with devices and to build the infrastructure to be able to connect everything. This is no trivial task and provides opportunities for both entrepreneurial and tech minds.
I have talked before about the coming Internet of Things and the changes it will bring. The Internet of Things or IoT is a term coined by Cisco to describe the interconnected nature of devices that are linked to each other and to the Internet or an intranet. Imagine a future where your car communicates with your refrigerator and your oven and your home heating, security, and entertainment systems. On your way home from work your car automatically detects your intended destination and communicates with your refrigerator to release your dinner to the oven. By the time you arrive home the lights are on, your security system has unlocked the door, and dinner is on the table, with soft music playing to soothe you after your hectic day. This is all well and good but it will require a lot of work in the background to embed all of these things with devices and to build the infrastructure to be able to connect everything. This is no trivial task and provides opportunities for both entrepreneurial and tech minds.
IPv4 vs. IPv6
If you think about how many items are produced every day worldwide and then consider that if even a small portion of those items are connected to the Internet you realize that adds up to a lot of unique Internet identifiers or addresses. In the early days of the Internet, a system was developed which provided for unique Internet protocol or IP addresses for every computer. Currently, version 4 or IPv4 allows for a maximum of 232 or 2.4 trillion addresses. IANA, the world body assigned to distribute those addresses, reported that the last block had been given out in February 2011 and the remaining addresses are now in the hands of five regional distributors.
Internet Protocol version 6 (IPv6) allows for a maximum of 2128 unique addresses. In theory, it should be enough to cover all computers, tablets, smart devices, and “things” for the foreseeable future. Even though IPv6 was introduced in 1995, it is not yet widely used because of the complexity of conversion and the manpower needed for the task. This provides a huge opportunity for individuals who understand the conversion process and implementation procedures of the new addressing scheme. However, much work needs to be done, and it is not just a matter of flipping a switch.
Embedded devices
There are ample opportunities for entrepreneurs who can not only come up with a way to embed devices in everyday things but also those who can develop the interconnection between devices and who can do a deep dive in to the data to create meaning. There are three important steps that need to take place to make the Internet of Things a reality:
- Devices need to collect various data points such as a manufacturing process or a patient status or the geospatial position of a package.
- Those data points need to be collected, probably in the cloud, and/or shared with other devices, smart or otherwise.
- The collected data needs to be analyzed to affect improvements to the whole cycle. Without this deep analysis, the data will be useless to decision makers.
In all three of these areas, I see opportunities for enterprising minds that already have these skills or are willing to develop them to be out in front of the Internet of Things.
Thoughts
Do you have ideas for everyday things that you wish could communicate, such as your car keys when they are lost, or your car in the mall parking lot during the Christmas shopping season? Some of these are already becoming a reality. It’s your turn to develop the next connected device or help develop the back end infrastructure that will collect and process all of the new data points to improve our work and our lives.
About Kelly Brown
Kelly Brown is an IT professional, adjunct faculty for the University of Oregon, and academic director of the UO Applied Information Management Master’s Degree Program . He writes about IT and business topics that keep him up at night.

